Vercel’s Security Announcement
On April 19, Vercel released a security notice on their official website. The wording was restrained: “We have discovered a security incident involving unauthorized access to certain internal systems of Vercel, affecting a limited number of customers.” The announcement also revealed that the company has hired external incident response experts to investigate and has notified law enforcement.
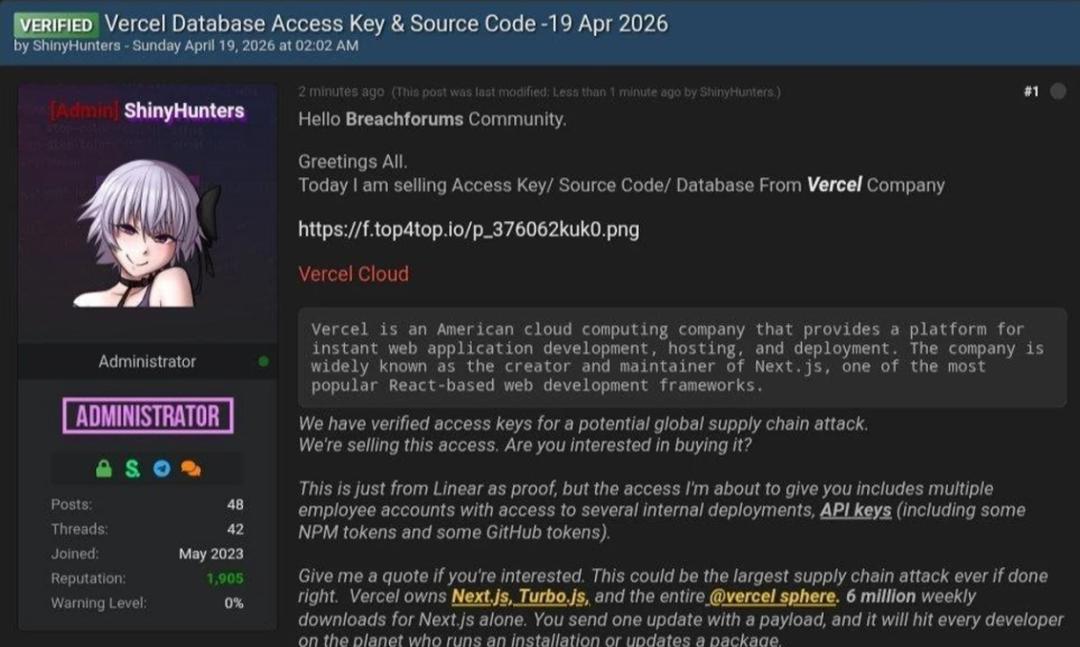
Shortly after, a post appeared on the dark web forum BreachForums, where the poster claimed to be a member of the notorious hacking group ShinyHunters. They asserted that they had obtained Vercel’s internal data and were demanding $2 million, with an upfront payment of $500,000 in Bitcoin. As proof of “cash on delivery,” they released a text file containing 580 records of Vercel employees, including names, company emails, account statuses, and activity timestamps, along with a screenshot of what appeared to be an internal corporate management backend.
The timing of this incident is notable. The event occurred over the weekend, and many Vercel users first learned about it from a post on Hacker News, prior to receiving direct notification from the company.
How Did the Attackers Gain Access?
The answer lies in a statement made by Vercel CEO Guillermo Rauch on X afterward. The entry point was not Vercel itself, but a third-party AI tool used by an employee, Context.ai. The attackers gained access to the employee’s account through a Google Workspace OAuth application associated with Context.ai, subsequently gaining lateral access to Vercel’s internal environment.
This reflects a typical attack vector today: entering through a side door rather than the front, with that side door being a trusted AI integration tool.
What is Vercel and Why This Matters Beyond One Company
For many, the name Vercel may be unfamiliar. However, if you’ve used any web application rapidly generated with AI, it is likely deployed on Vercel.
Vercel is a “frontend cloud platform” for developers. You write your code, push it to GitHub, and Vercel automatically compiles, deploys, and goes live, with global CDN acceleration, requiring almost no operational knowledge. It is also the official maintainer of the popular React framework Next.js, which currently sees about 6 million downloads per week. In the wake of the AI programming wave, Vercel has become one of the core infrastructures in the “Vibe Coding” ecosystem. Vibe Coders are developers who use AI tools like Cursor, Claude, and Bolt to quickly generate code and create product prototypes using natural language. They may not have traditional engineering backgrounds but can turn an idea into a functioning website in a matter of hours.
The most common tech stack for such projects typically involves Vercel for deployment and Supabase for database management. The former handles “how to go live with code,” while the latter addresses “where to store data.” Both emphasize “zero operations,” making them the default choice for Vibe Coders.
This is why the impact of this incident extends far beyond the data security of a single company. Many cryptocurrency and Web3 projects have their frontends deployed on Vercel, from wallet connectors to decentralized application interfaces, potentially storing API keys, private RPC endpoints, and wallet-related keys in environment variables. If these credentials are leaked, the potential losses could be more than just data; they could involve real assets.
The Real Danger of “Non-Sensitive” Variables
A key distinction in the details of the incident is worth clarifying. Vercel’s system classifies environment variables into two categories: those marked as “sensitive” are encrypted and cannot be read, while ordinary variables without such marking are relatively exposed. The attackers were able to read these unmarked ordinary environment variables. Vercel stated that there is no evidence that variables explicitly marked as “sensitive” were accessed.
The issue is that this “sensitive” marking has long relied on developers’ judgment and actions. Many Vibe Coders, as well as experienced engineers, may not assess the risk level of each value when configuring environment variables. Database connection strings, API keys for third-party services, GitHub access tokens—these items are often casually placed into variables without being marked as “sensitive.” The platform’s security mechanisms are intact, but they depend on correct user operations to be effective.
Security researchers have long warned that even seemingly harmless configuration data can provide attackers with a foothold to access downstream services with broader permissions. “Non-sensitive” often reflects internal classification strategies rather than actual exploitable risks. This highlights a classic issue: platform security does not equal user security.
The Ghost of Supply Chain Attacks
What unsettles the security community most about this incident is not the 580 employee records, but the potential pathways hinted at by ShinyHunters in their post. If the attackers truly gained access to Vercel’s internal build system, they could theoretically tamper with the Next.js packages pulled by millions of developers each week, leading to a supply chain attack. Vercel later confirmed that Next.js and its supply chain are currently unaffected by this incident. However, the mere possibility raises serious concerns.
The 2020 SolarWinds incident serves as a textbook case of a supply chain attack: attackers infiltrated a software build system trusted by thousands of companies, pushing malicious code through normal updates to all users, with the vulnerability remaining undiscovered for months. Vercel’s situation is structurally similar. It is not just an IT system for one company, but a pipeline for building and deploying thousands of web applications.
This is also the logic behind ShinyHunters’ asking price of $2 million: they are not just buying data, but potential “leverage.”
Key Takeaways Beyond Vercel
Several parallel realities emerge:
-
The entry point was a third-party AI tool. The Google Workspace OAuth application of Context.ai was compromised, allowing attackers to infiltrate Vercel’s internal environment. This means the true target of this attack may extend beyond just Vercel. Other companies using the same AI tool face similar risks.
-
This incident surfaced just before Vercel’s planned IPO. In the days prior, reports highlighted Vercel’s revenue growth of 240% year-over-year, driven by widespread adoption of AI deployment workflows by enterprise clients. A security incident combined with communication restrictions during the quiet period before an IPO sends a complex signal to investors.
-
There is a broader industry signal. In today’s AI ecosystem, every developer’s toolchain integrates numerous third-party AI services for code completion, context retrieval, documentation generation, and log analysis. These tools connect to developers’ GitHub, Google Workspace, and internal systems through OAuth authorization. Their security has not undergone large-scale scrutiny like AWS or GitHub.
Vibe Coders are accustomed to rapid integration and deployment, often considering security configurations as an afterthought. The Vercel incident serves as a reminder that this long-ignored issue has now come to the forefront.
Entering through AI tools rather than the front door may become one of the most common enterprise intrusion pathways in the coming years.
Comments
Discussion is powered by Giscus (GitHub Discussions). Add
repo,repoID,category, andcategoryIDunder[params.comments.giscus]inhugo.tomlusing the values from the Giscus setup tool.